I don't know for a fact that the keychain file backed up on Google Drive was the hacker's entry. In any case, corrective action was taken.
I can't think of any app I tried that managed to fool me into giving up my PEPT key(s).
I don't know why the PEPT account was the target or why I was a target.
I do know there is still a scammer(s) out there looking to steal Hive and send it to a Binance wallet.
Thanks you for the suggesting and support in Hive discord.
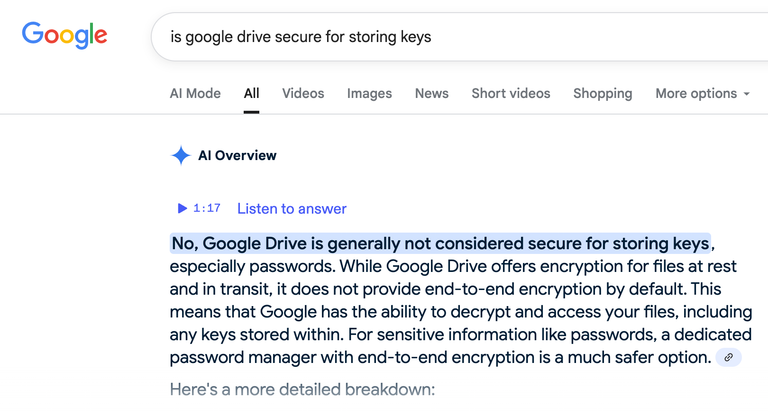
Simply having the pept.json file compromised on google docs would not be enough to gain access to the funds since the keys in the keychain file are encrypted. Therefore an attacker would also need to know the master password, however, if the master password was weak or the computer is compromised by a keylogger, the attacker could obtain both the file and the password, leading to a complete compromise of the account.
Another possibility is that an attacker got the encrypted keys on google docs, and then brute forced the master. Sounds a little bit far fetched, but depending on the length of the master password I suppose it could be possible.
Or a more likely possibility is that someone broke into your house, got onto your computer and did the transfers, maybe a stalker or someone you know or might have seen you on hive?
For the record, I didn't store keys inside a Google doc.
I found a backup txt file and the keychain kc file on my Google drive.
Out of curiosity, when credentials are exchanged between keychain app, or any apps, and a user, is there some server session cookies at play? If so, could a server session cookie be highjacked?
Nope, there are no server session cookies involved when credentials are exchanged between a user and a keychain application. These apps are designed to be secure, client-side storage vaults. Keychain is an encrypted database stored locally on your device. When you save a password, the app encrypts it using keys derived from your device's hardware and your passcode. This makes the data incredibly difficult to access without physical access to the device and the correct password or biometric authentication (like Face ID). When an app needs to access a credential, it requests it from the keychain. The operating system handles the entire process locally without sending the data to a server.
Thank you very much for that explanation.
Much appreciated.
!PIMP
!LOLZ
!SLOTHBUZZ
I still wonder what she saw in him.
Credit: reddit
@coininstant, I sent you an $LOLZ on behalf of fjworld
(2/10)
Farm LOLZ tokens when you Delegate Hive or Hive Tokens.
Click to delegate: 10 - 20 - 50 - 100 HP
